
iPhone 16 rumors: release date speculation, design leaks, price outlook, and more
The iPhone 16 is expected to arrive later this year, and here's everything we know about Apple's device so far.
Get our in-depth reviews, helpful tips, great deals, and the biggest news stories delivered to your inbox.

By Sean Riley last updated
Picking the best MacBook is a tough call, but we've tested and reviewed every model to make sure that you know which Apple laptop you should buy.

By Stevie Bonifield published
Ori and the Blind Forest meets Black Panther in this inspiring fantasy platformer

By Rael Hornby published
The Anker Nebula Mars 3 Air is proof that good things come in small packages, bringing a cinema experience into the home with spacious audio, quality pictures, and a hassle-free setup.

By Stevie Bonifield published
The Endgame Gear OP1 8k gaming mouse is a weightless speed demon

By Rami Tabari published
The Dell XPS 14 offers excellent performance and graphics packed into a sci-fi design you’ll fall in love with for roughly 10 hours per charge, but I’m still upset about its dull display.

By Madeline Ricchiuto published
A stylish, reliable, premium laptop held back by a few sub-par features like a dim display, grainy webcam, and a soft keyboard.

By Momo Tabari published
The Akko Sailor Moon Crystal 5087B v2 gaming keyboard excels with soft PBT caps, an adorable aesthetic, silent but satisfying keypresses, and customizable per-key RGB lighting.

By Rami Tabari published
You don't have to pay $3,500 for the Apple Vision Pro, and you don't have to wait any longer for an affordable version. Here's why you should consider the Meta Quest 3 and Meta Quest 2.

By Sarah Chaney published
Horizon OS is getting a new spatial framework that will let mobile developers easily bring existing or new apps over to Meta's Quest headsets or any new headsets running Horizon OS.

By Hilda Scott last updated
Everything you need to know about this year's Memorial Day sales including run dates, what stores have sales, what you should buy on Memorial Day, more
By Momo Tabari published
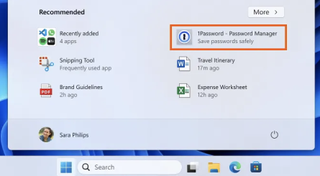
Windows 11 released a software update yesterday that places advertisements on the Start menu, with the changes gradually rolling out to users throughout the week. Here's how to turn them off.

By Hilda Scott last updated
The best tablet deals from a variety of retailers. Save big on today's best tablet PCs.

By Mark Anthony Ramirez last updated
After years of rumors and speculation, it seems Apple might finally be ditching those clicky buttons for a sleeker, more modern approach.

By Stevie Bonifield published
Why are Apple Vision Pro sales declining already? Apple's pricey headset has a few big issues holding it back, but it might not be too late for Apple to turn things around.